Key Judgements
KJ-1. Ryuk ransomware attacks vastly increased during 2020. From almost obscurity in 2019, Ryuk now accounts for a third of all ransomware attacks.
KJ-2. UNC1878 is the threat actor behind the largest percentage of all Ryuk ransomware attacks according to FireEye. They are a financially motivated group.
KJ-3. The timing of the attacks is almost certainly not down to chance. It is almost certain that the large increase currently in Ryuk ransomware attacks are due to current political conditions, along with the targeting of hospitals during a pandemic.
What happened?
On the 28th of October 2020, the United States Cybersecurity and Infrastructure Security Agency (CISA), the FBI and the Department of Health and Human Services (HHS) released a cybersecurity advisory update given recent ransomware attacks on the American health sector.
The attacks follow on from what has been an exceptionally active year for Ryuk ransomware attacks. In the third quarter of 2020, SonicWall has observed a 40% increase in ransomware attacks, with the United States seeing a 139% year on year increase in ransomware attacks. Through these attacks, Ryuk has seen a massive increase in usage. Over the first three quarters of 2020, there were 5,123 observed Ryuk attacks. Up to the third quarter in 2020, there have been 67.3 million detected attacks by SonicWall. These attacks make up a third (33.7%) of all ransomware attacks so far this year.
A massive increase observed by SonicWall in September concerning ransomware is in line with a large Ryuk ransomware attack on the Universal Health Service (UHS) in the United States. After an attack on the 28th of September 2020, UHS shut down computer systems across the United States. UHS is estimated to care for 3.5 million patients a year at over 400 locations in the United States and the United Kingdom.
Although UHS was likely the largest victim of a Ryuk ransomware attack so far within the United States health sector, this is a growing concern across the entire industry. Sky Lakes Medical Centre in Oregon, WA was the target of a Ryuk ransomware attack on the 27th of October 2020, the day before the cybersecurity advisory update was released.
Threat Actor UNC1878 & Ryuk
Mandiant, the incident response wing of FireEye, has traced the origin of a large percentage of Ryuk ransomware attacks to a threat actor named UNC1878. In a report released on the 28th of October 2020, UNC1878 was described as:
“conducting these campaigns have actively targeted hospitals, retirement communities, and medical centres, even in the midst of a global health crisis, demonstrating a clear disregard for human life.”
UNC1878 is a financially motivated threat actor that has been observed since January of 2020. Mandiant threat analysts Aaron Stephens and Van Ta and have released UNC1878 indicators to GitHub.
Ryuk attacks are often deployed from Trickbots, a form of Trojan virus. Ryuk ransomware was first observed in August of 2018, stemming from another form of malware, Hermes (2.1). Often the ransomware will not be detected on a system until well after an infection has been placed into a system, allowing the threat actor to inspect the system.
Ryuk has been used to attack specifically enterprise systems, the key difference between itself and Hermes, from which it originated. It is believed that since its inception in 2018, actors using Ryuk have procured 705.80 Bitcoin (BTC) over 52 instances.
To observe how fast UNC1878 moves, the Time to Ryuk (TTr) is key. TTr is the time from when UNC1878 is in a target environment, to the delivery of ransom demands. FireEye and Mandiant have observed that the average TTr for UNC1878 to be five days and 17 hours, with the fastest time being observed being two days and 6 hours. The shortest time observed between domain registration and activity on a target system is 27 hours.
Ryuk ransomware attacks, hold a targeted system ransom until a payment is made to the threat actors. The ransom demands are often left in a RyukReadMe.txt file. The demands are often the same across attacks, with only email addresses and Cryptocurrency (almost certainly BTC) wallets changing.
Ransom demands can change drastically. Known demands have ranged from 1.7 BTC to 99BTC. Although BTC exchange rates vary, 1BTC on the 9th of December 2020 costs £13,385,41 on Coinbase. Should a Ryuk demand be received at the time of publishing, it could cost an organisation anywhere from £22,755.20 to £1,325,155.59.
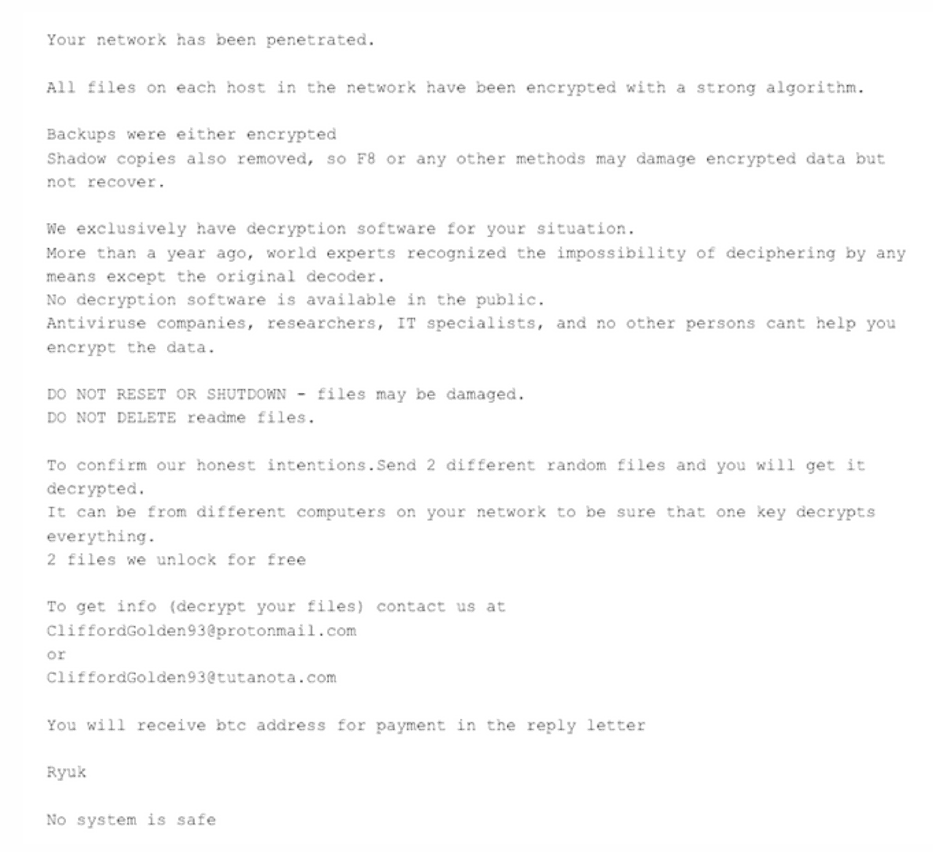
Example of a Ryuk attack ransom note.
Outlook
Given the current COVID-19 pandemic, the timing of the cybersecurity updated from CISA, the FBI and the HHS with credible information of increased threats to hospitals in the United States is a cause for concern. With the warning, hospitals and health organisations must follow the advice of the update and increase cybersecurity throughout the health systems at risk. The advisory from CISA details the best practices to prevent an attack, along with guidance from CI security.
Although Ryuk attacks are not new, and the scale of current attacks are certainly at a high, the situation surrounding the attacks are a cause for concern. The timing of the attacks is a cause for concern due to:
- Attacks against hospitals in a pandemic as cases are only increasing
- Specific targeting of American health care institutions during the closing period of an election cycle
- The FBI, CISA and the HHS confirming the legitimacy of the attacks
The timing is almost certainly not due to chance, but a coordinated attack to disrupt the American health care system and to financially gain as much as possible.
These ransomware attacks are coming only a week after it was thought that a joint Microsoft and Department of Defense Cyber command attempt to counter Trickbot ahead of the Presidential election in the United States. With Microsoft claiming to have shut down 120 out of 128 servers they believed to be part of Trickbots infrastructure, the attack on the Sky Lanes Medical Centre is a worrying sign.
Conclusion
In the wider context of cybersecurity, there has been a massive increase in ransomware attacks in general through the third quarter of 2020, with a third of attacks being Ryuk. The main threat actor behind the recent attacks are UNC1878, who are financially motivated threat actors. This group is known to work at a very fast pace. Most ransomware demands are in Bitcoin and can vary wildly in price. It is almost certain the attack timing, during the end of an election cycle in the middle of a pandemic where there is currently a rise in cases, are not by chance, and that it is designed to extort as much financial gain as possible.
Image: Pixabay
Image2: Crowd Strike (link)